US president Donald Trump likes to brand news from some publications and broadcasters as ‘fake news’ when they’re unfavorable to his character. The world can now expect to see fake Donald Trump themed ransomware arriving in email inboxes that attempts to con victims into paying a fee to decrypt files that were never encrypted. But it can install malware from filed called ‘trump.exe’.
Whatever your opinion of Donald Trump, the chances of avoiding images of his face just got a bit smaller with scammers now capitalizing on his brand to deliver malware in spam that locks a PC to a screen that displays the current US president’s face with a ransomware message.
Cisco Talos Intelligence malware researchers say they recently found several examples of fake ransomware and screen lockers that featured images of Trump.
“These samples didn't always encrypt the data properly or at all, but nonetheless, they could lead users to believe that their data was lost. Victims could also be tricked into paying a ransom demand in an attempt to regain access to their data, generating revenue for attackers,” wrote Cisco’s Nick Biasini and Edmund Brumaghin.
The cybercriminals and scammers aren’t just exploiting the Trump brand to package their malware, but also the image of Russian president Vladimir Putin via lock screen messages which state that “PuTiN Lockware has locked your pc.”
Instead of an image of the president’s face, as was used in the fake Trump ransomware, the Putin non-ransomware message is displayed over a grid of burning skull and crossbones.

The fake Putin ransomware does not meet the bar for the worst ransomware since it didn't actually encrypt files, but rather locked the screen and removed desktop icons, the task bar, and the task manager on affected machines. Victims are then directed to contact the attacker by email and negotiate a payment.
According to researchers at Cisco Talos Intelligence, the politically inspired malware attacks are initiated through mass spam campaigns.
“The emails associated with this campaign purport to be related to banking fraud and are made to appear as if they were sent by the director of Global Risk for credit card company Visa,” noted Cisco.
The malicious spam campaigns have emerged as the US presidential 2020 mid-term election campaigns kick into full swing.
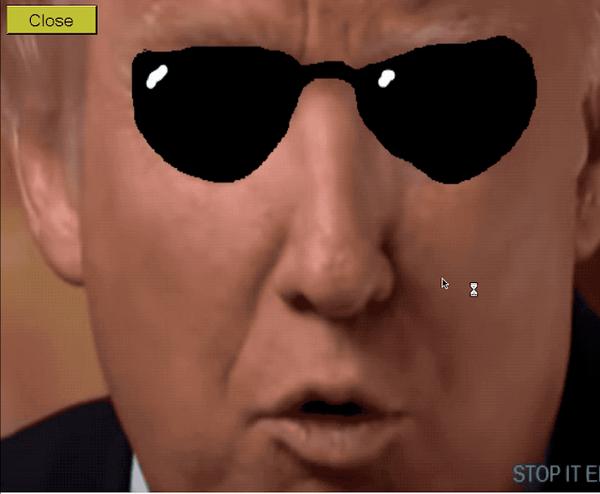
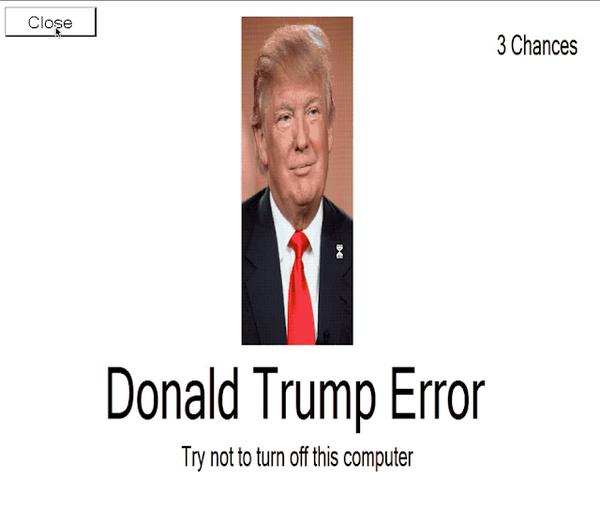
Another Trump-themed locker warns users of a “Donald Trump Error” and advised victims to “Try not to turn off this computer”. If the victim does close the screen, they're presented with the "Donald Trump Error" message.
After seeing Trump in fake shades, the victim is then presented with the “Donald Trump Screen of Death” -- a nod to the Microsoft Windows “Blue Screen of Death”.
Cisco notes a few oddities with the Trump malware. First, the attacker didn’t offer a way to remove the malware, meaning there’s no opportunity for an exchange between victim and attacker. State-sponsored attackers behind the NotPetya malware used a similar tactic, veiling file destroying malware as ransomware. Additionally, clicking on the screen removed the locker and the system continued to operate normally, potentially indicating the malware was just a hoax.
Cisco also found links in this malware to past activities by state-sponsored attackers.
“One of the unexpected aspects of the investigation was the presence of lures that dropped malware associated with multiple nation-state attacks in the past, showing how even advanced, sophisticated adversaries will use any means to achieve their nefarious goals,” wrote the Cisco researchers.