GoDaddy's layered verification protections defeated by a phone call and four hours in Photoshop
On Tuesday, my personal account at GoDaddy was compromised. I knew it was coming, but considering the layered account protections used by the world's largest domain registrar, I didn't think my attacker would be successful.
I was wrong. He was able to gain control over my account within days, and all he needed to do was speak to customer support and submit a Photoshopped ID.
GoDaddy serves more than 13 million customers, who in turn place 59 million domains under the registrar's management. They have thousands of employees working across the globe who help staff the support and operations teams twenty-four hours a day.
Sometimes, customers forget their account number or password; perhaps they forget what email they've used to register a domain. In either case, GoDaddy's support staff are there to assist.
According to GoDaddy support, account resets are a simple process. If you've forgotten your username or customer number, you simply select the correct link at the login screen or account assistance page. However, you can also call customer support and complete the process over the phone.
Depending on the circumstances, a phone call will resolve most account related problems, provided you know your domain, the email address on file, customer number (or username), street address on file, or the last four digits of the credit card used on the account.
When Vinny Troia, the CEO of Night Lion Security, called GoDaddy and attempted to reset my account password, the representative who answered the phone followed all established protocols and attempted to confirm Mr. Troia's identity.
Armed with only basic information and no access to the account's primary email address, Mr. Troia should have failed. Yet, the exact opposite happened; he succeeded despite GoDaddy's layered protections.
"Initiating the takeover was a relatively simple process. I called GoDaddy and explained that I no longer had access to my domain. We reviewed and verified the WHOIS information - which really consisted of me reciting the WHOIS information back to the representative," Mr. Troia said, explaining the process of compromising my account.
"She asked if I had access to the email address on file, which I obviously did not. I explained that there were a lot of office politics at the moment that I didn't feel like getting into. Long story short, it was my domain and I wanted access to it."
While this conversation was taking place, Mr. Troia's daughter was making noise while playing. This background distraction created just the setting needed for Mr. Troia to push his social engineering scheme. By acknowledging the distractions, it was clear that Mr. Troia had a good deal of things going on, so the support representative was more than happy to move the conversation forward and make the process painless.
People are always going to be the weakest link in the security chain.
However, people in a service or support role are unique. Their job is to make things easy for the customer. They're not paid to judge and it's uncommon for them to be allowed to deny a customer request based on suspicion alone.
While awareness training can help, it isn't a perfect solution for those working in customer service, because regardless of their suspicions, most are bound to support the customer first and foremost.
Some organizations do empower employees to deny requests if they feel there is a security risk. At the same time, the process of denial requires considerable effort on the support employee's part. It's easier, and far less stressful to simply make the customer happy and do as they ask within reason.
Resetting a username and password seems reasonable, provided the customer isn't being pushy and can justify a lack of information. That's what Mr. Troia did. He justified a lack of information by playing the frustrated executive.
"She asked me to verify the PIN, which I didn't have. She then asked me to verify the last four digits of the credit card used to purchase the domain, which I also didn't have. I explained to her that I'd asked my assistant to setup the domain for me," Mr. Toria said, continuing his explanation.
Mr. Troia told GoDaddy's support representative that his "assistant" had said he'd used a card ending in four random numbers. The numbers he gave the representative were made-up on the spot. Naturally, those numbers were incorrect and that verification step failed. Adding to this, the support representative was told that the assistant didn't remember setting up a PIN.
"I apologized, both for not having the information and for my daughter yelling in the background. She laughed and said it wasn't a problem. I was directed to a website where I could fill out a form and request access," Mr. Troia said.
If none of the account information is available during a reset request, GoDaddy will allow customers to use a change of account (or email) form.
This form requires that you provide a copy of a government-issued ID, such as a passport, military ID, or driver's license, in order to prove you're who you say you are. If the domain in question isn't a personal domain, then business information is required as well. The entire process is completed online, and full instructions are available here.
In order for the attack to work, Mr. Troia created a fake Gmail account, as well as a Google + profile to match his version of Steve Ragan. The email account would be used for password resets. The social media account was simply there to give Troia's Steve Ragan a presence on the Web.
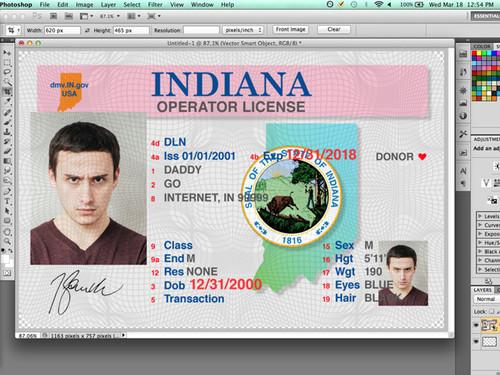
When it came to government-issued identification, he turned to friends in Indiana.
"I knew a few people in Indiana and they both sent me quality pictures of their license. In the end, I found it easier to modify their existing license than to make a new one from scratch. I spent about four hours with the details of the license and getting the shading of the text right.
"This was probably overkill, but I'm a perfectionist when it comes to these things. The subtitles in the driver's license seal were no match for Photoshop's 'content aware and replace' feature. It wasn't perfect, so the majority of my time was spent pushing pixels until it looked right. A little blur and grain go a long way to making something look authentic," Mr. Troia said.
The form was submitted on Friday, March 13, but it wouldn't be reviewed until the following Monday, as those responsible for change requests do not work during the weekends.
On Tuesday afternoon, Mr. Troia received an email asking for additional information. Most of the domains under my account are registered to a business name, which would require additional information.
"I sent an email stating that there was no actual business which they could verify, and that I just put something there because I thought I had to. I sent the email and immediately called right after. The woman I spoke with was super nice. She looked at the email while we were on the phone and said that people use non-existent business names all the time. They just needed the written copy for an audit trail. She authorized the email switch while we were on the phone. Instructions to reset my account password were in my email by the time we hung up," Mr. Troia said.
What happened to my account is something that could happen to any account.
There was no document verification performed and the ID submitted by Mr. Troia used an image that looks nothing like me. From social engineering, to the crafted social media profile, fake ID and email account, this was a classic example of a targeted attack from start to finish.
An account takeover such as this allows an attacker to use the hijacked domain to create code-signing certificates. It could be used to impersonate someone's personal brand, and leverage said brand to target customers, fans, or business partners.
An attacker could develop any number of domains and use them for a watering hole attack, or alter DNS and direct visitors to a server under their control.
In fact, such tactics are a favorite of groups such as Lizard Squad and the Syrian Electronic Army, who target hosting accounts for exactly those reasons.
"If [the attackers] wanted to be slick about it, they could gain access, insert their code, create backdoor admin accounts, and return access back to the original owner before they even knew what had happened. The owner would receive the confirmation email, see that their website is still online, and consider it a Phishing attack and just delete it," Mr. Troia said.
GoDaddy isn't the only major domain registrar to use photo ID as a last resort. Network Solutions also has an ID-based verification, but unlike GoDaddy, the ID and required documents must be faxed over, instead of uploaded. Interestingly enough, one domain registrar, Hover.com, doesn't allow photo ID as a form of verification, because "anyone could just whip something up in Photoshop."
Using GoDaddy's DomainControl and privacy features, which are offered as a value-added service for an additional cost, would only slow a determined attacker. While the public can't see the registration details, the support staff can. So an attacker armed with public information could abuse the change of account form.
Mr. Troia hopes that by exposing the logic flaw in their security model, GoDaddy will implement tougher verification procedures, but admits it's a paradoxical situation. A valid government-issued ID should be an acceptable form of verification, but it's clearly not enough.
Two-factor authentication isn't viable either, he said, because if someone hijacks the domain and enables that protection after the fact, then the customer would be left with few options for reacquiring access to the domain.
"The reality is that if I register a domain, I should have some idea of what credit card was used to pay. In your case, the domain was registered a few days ago, so it's not as if I would have no record of it. I could have pulled up my bank statement and gotten the last four digits," he said.
"This [change of account form] probably exists to help the customer gain access to their domain in the event of an issue, but we have clearly shown that there isn't enough security to protect the customer from having their domains stolen."
GoDaddy did attempt to contact me via email and inform me of the registration changes, including the new DNS settings that Mr. Troia applied to a domain recently purchased for this story.
Unfortunately, that email came long after he had reset the account password. A follow-up email didn't arrive until nine hours later. If this attack had been real, it would have been too late. The domain where the GoDaddy warning was sent is on the same account that was compromised.
So what can consumers and organizations do to protect themselves from this type of attack?
"The best thing you can do is setup domain privacy, which makes it more difficult because I would need to find the private contact information, which can easily be done with DomainTools; then go through DomainControl.com or whichever company is keeping the domain private," Mr. Troia explained.
"Do your due diligence. If you're really worried about the security of your domain (as you should be), find out what security protocols the registration company has in place. Ask your registration (or hosting) company what safeguards they have in place in case your account is hijacked. How will you get it back? Hacking is pretty common now, so they should have an answer ready."
When asked for a comment on this story, as well as answers to a number of pointed questions on the limits of their customer support staff and the existence of an account reset form, GoDaddy only responded with a single statement:
"GoDaddy has stringent processes and a dedicated team in place for verifying the identification of customers when a change of account/email is requested. While our processes and team are extremely effective at thwarting illegal requests, no system is 100 percent efficient. Falsifying government issued identification is a crime, even when consent is given, that we take very seriously and will report to law enforcement where appropriate."